Submission and audit lifecycle
End-to-end narrative
- Draft — You build a draft in the portal: category and complexity drive later quotes (see Payments and pricing).
- Quote — Pricing rules, campaigns, and first-N promotions come from the operator catalog.
- Payment — You create and confirm a payment intent (direct Monad and/or x402, depending on what is enabled).
- Submit — Finalize into a live submission; size and manifest limits apply per deployment.
- Sandbox — Background workers run heuristic checks; failures surface as rejections with reasons operators can see.
- Audit round — Two-phase validator assembly; validators are assigned per protocol rules; each produces a managed-model verdict with advisory plugin XML.
- Consensus — SAFE / UNSAFE patterns are merged with sandbox source signals; splits and high-risk signals escalate rather than certifying by default (see Assembly and reputation).
- Certificate — Approved work seals a certificate snapshot; deployments expose canonical payload hashing and may record on-chain commitments where enabled; public verify surfaces publish hash and commitment state (see Verification and trust boundaries).
Risk posture remains proportionate: SIGMA is a verification product, not a proof of complete absence of vulnerabilities for every threat model.
Audit flow diagram
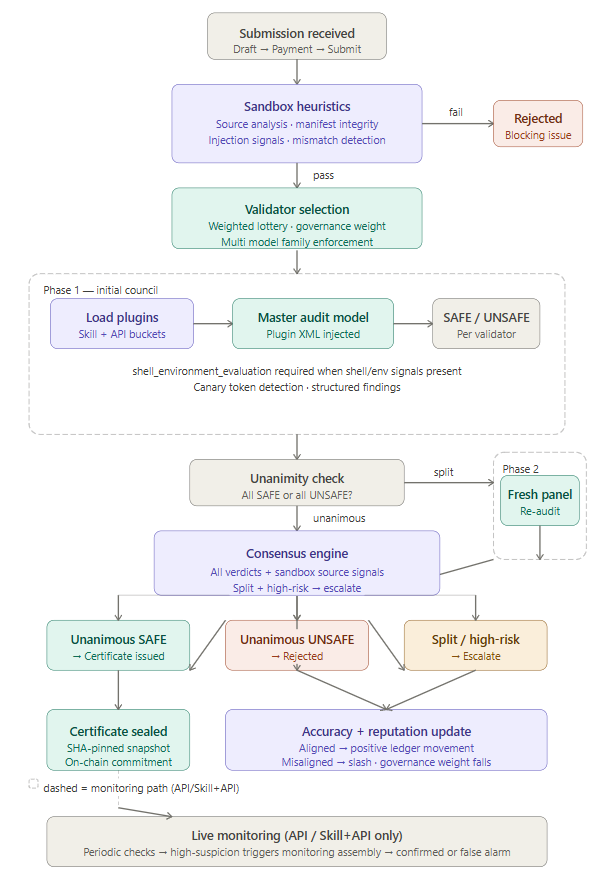
Assemblies, consensus, and standing
Assembly means multiple validators and phases contribute verdicts before a submission is approved. The engine resolves SAFE / UNSAFE patterns together with sandbox source signals; split votes and high-risk signals can escalate instead of forcing a weak certificate. Participating validators who end up misaligned with the final scored outcome lose audit-accuracy signal; SIGMA reputation reflects longer-run trust and also moves down on poor assemblies, low-quality patterns, and operator-class sanctions — see Assembly and reputation and Verification and trust boundaries.
Validator plugins
During verdict construction the system loads active SIGMA plugins for the auditing validator and wraps them in <validator_analysis_plugins>. Skill-shaped submissions get skill nodes; API-shaped submissions also get API nodes. Rules: Runtime injection.
Usage counts
Each injection can increment public usage on the plugin and write an operator-only usage log (phase, submission type, verdict).
Legacy skills
Older dev-portal skill assignments may still run a separate augmentation step. That path does not increment usage on the new plugin system—do not merge the two metrics blindly.
Operators
Where policy allows, operators can override or re-audit. Developers can open support or human intervention—see Manifests and wallets and Payments and pricing.